Using Cluster Api to Create Kubernetes Clusters on Azure
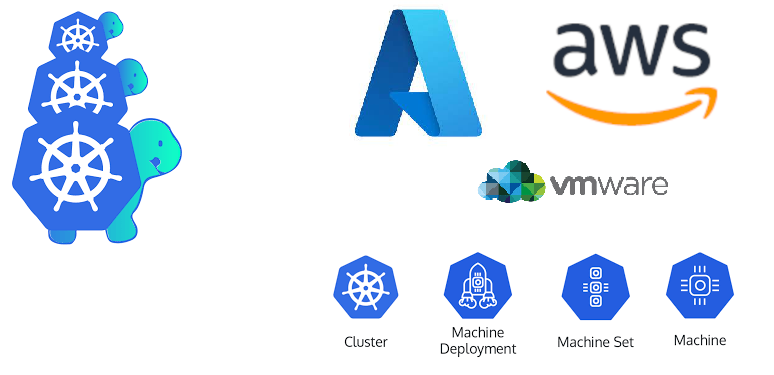
In this post let’s look at using CAPI to deploy a Kubernetes cluster in Azure. The end goal is to create a Kubernetes cluster in Azure with three control plane nodes and three worker nodes.
In this post let’s look at using CAPI to deploy a Kubernetes cluster in Azure. The end goal is to create a Kubernetes cluster in Azure with three control plane nodes and three worker nodes.
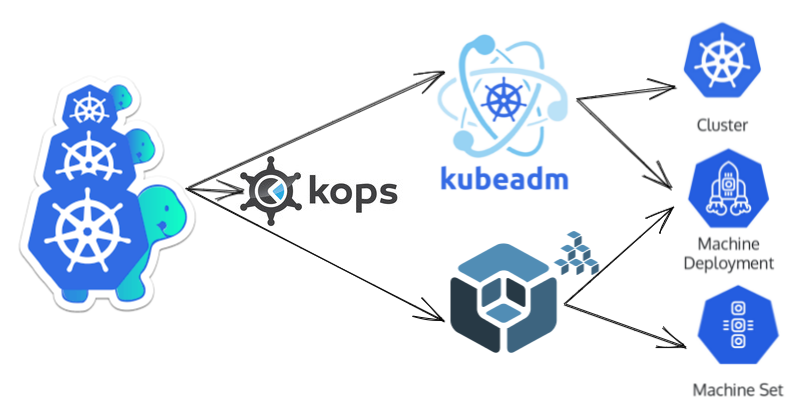
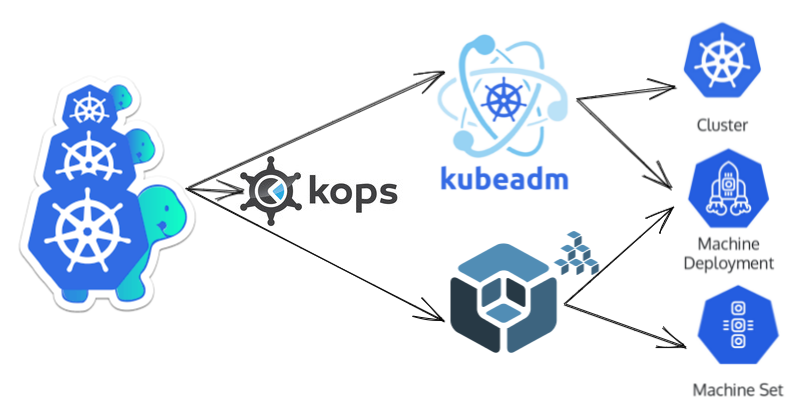
Cluster API brings declarative, Kubernetes-style APIs to cluster creation, configuration, and management.

I have been part of a couple of build outs where we built Kubernetes clusters to run our cloud workloads. These builds involved deploying AKS clusters using terraform and AzDO. Designing the AKS infrastructure is key to ensure that the cloud workloads running on them can be deployed, secured, and hosted effectively. In this post I am documenting the general steps involved in building out a Kubernetes infrastructure on Azure Kubernetes Service (AKS) using terraform and deploy workloads using Azure devops (AzDO) and Helm charts. ...

GraphQL is a query language for APIs. It is a query language that provides for client-tailored queries. It is an API specification.
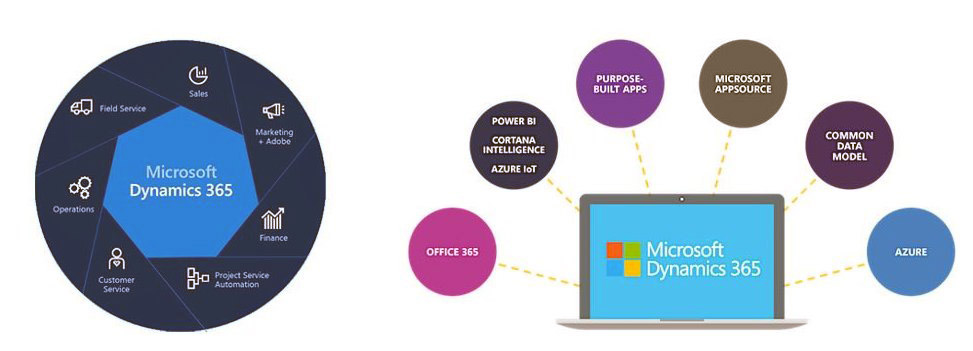
Dynamics 365 for Finance and Operations is designed and architected for the cloud. It can be deployed as an on-premises system or on the cloud.

Creating Cosmos Db Infrastructure The azure Cosmos DB team provides SQL API SDK’s for various languages. At the time of writing this post the NuGet package for .NET core is at version 4 preview 3. The GitHub repo for this NuGet package is here . To get started we can use the Cosmo Db emulator locally or create a Cosmos Account on Azure. We can log onto Azure portal to create a Cosmos Account or use Azure CLI. I am using the below Azure CLI command to create a Cosmos DB account. This command creates a Cosmos DB Account named eCommerceDb-AC in the eCommerce-RG resource group. ...
It is imperative to understand core concepts involved in modelling data in Cosmos Db to harness its power. It is an extremely powerful cloud native database.

Cosmos DB is a cloud native database engine on Azure. It is a born-in the-cloud database with no legacy compatibility requirements. It can expose data using a variety of models and API’s.
Sunshine coast .Net user group meeting. Topic - Getting started with terraform on Azure.
Sunshine coast .Net user group meeting. Topic - Getting started with terraform on Azure.