
Securing the Software Supply Chain: A Developer's Guide
Learn how to secure the software supply chain by embracing best practices such as secure coding, CI/CD integration, SBOMs, and proactive monitoring.

Learn how to secure the software supply chain by embracing best practices such as secure coding, CI/CD integration, SBOMs, and proactive monitoring.
Master SQL Server to PostgreSQL migration with our comprehensive guide covering schema conversion, data migration methods, testing strategies, and optimization - achieve 40-50% cost savings.

This blog post guides you through the process of generating SSL wildcard certificates using ACME challenges and Certbot, helping secure your domains with Let’s Encrypt.

Explore the power of model inference, its importance in machine learning, and best practices for getting the most out of your models.
Learn how to set up Greenplum on Rocky Linux in WSL2 and explore its powerful features for AI/ML workloads.
Step-by-step guide to configure NVIDIA GPU acceleration for TensorFlow on Windows WSL2. Covers CUDA 12.x installation, cuDNN setup, common errors, and verification - get 10-100x faster training.
Fraud detection involves finding patterns in data. In this blog post we will build an AI/ML model for fraud detection
Learn the fundamentals of AI and data science in this non-technical guide. Discover subfields like machine learning and robotics, and explore how to use AI for problem-solving.

ZTA operates on a fundamental principle - never trust, always verify. Lets understand what it is and how to implement it
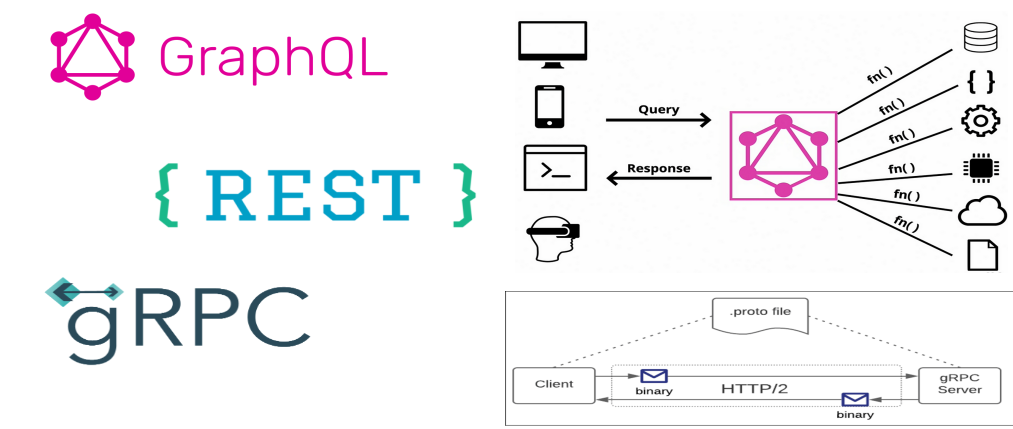
Three technologies stand out as primary choices for developing API’s REST, GraphQL, and gRPC. Understanding what they bring to the table and making sure it aligns with your API design goals is key in developing successful API’s