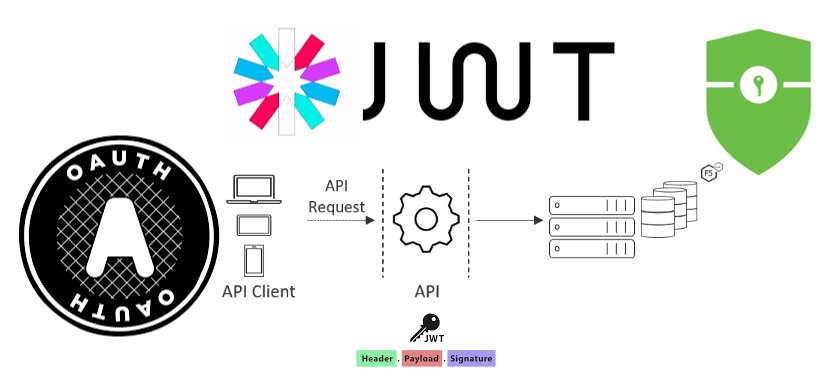
OpenID Connect is a simple identity layer built on top of the OAuth 2.0 protocol. OpenID Connect is all about authentication while OAuth is an authorization protocol. In OAuth, authorization is delegated while in OpenID Connect, authentication is delegated. OpenID Connect allows clients to verify end users based on the authentication performed by an auth server. It is also used to obtain basic profile information about the end user in a standards-based, interoperable and REST-like manner. OpenID Connect provides a standard way to obtain user identity.A central part of the OpenID Connect specification is the ID Token. It provides an identity token with information about the user. It also defines an endpoint to get identity information for that user, such as their name or e-mail address. This endpoint is called the user info endpoint. The identity token is a simple JWT token signed by the OpenID provider(OP) through OAuth protocol to suit web, mobile, and browser-based applications.The Identity token is encoded into the base 64 URL-safe string that contains information such as subject (sub), issuing authority (iss), audience (aud), and more. It may also contain some extra information about the user or custom claims in a set of scopes. As OpenID Connect is built on top of the Oauth2 protocol, the flows are the same. It can be used with the authorization code grant and the implicit grant. It’s not possible with the client credentials grant, as the client credentials grant is for server-to-server communication.As part of the oAuth flow, Instead of only requesting an access token, we can request an additional ID token from the security token service (STS) that implements the OpenID Connect specification. The client receives an ID token, and usually, also an access token. The ID token is kept small with the minimal information in it. To get more information for the authenticated user, the client can then send a request to the user info endpoint with the access token. This user info endpoint will then return the claims about the new user.
...